Free Coaching Lectures - Free NEET and AIIMS Coaching Lectures | Free Medical Entrance Coaching Lectures | Free CBSE Board Coaching Lectures | Free Biology Coaching Lectures | Free Physics Coaching Lectures | Free Chemistry Coaching Lectures | www.ConceptsMadeEasy.com
Use this Coupon to get upto 70% OFF on Hostarmada Affordable Cloud SSD Web Hosting Services
Following are the list of best awaresome videos on "Akzyrghp' Or 806=(select 806 From Pg_sleep(15))" which you can watch online here or download.
 SQL injection attack, querying the database type and version on Oracle | Web Security Academy
SQL injection attack, querying the database type and version on Oracle | Web Security Academy
Web Security Academy Lab: ... DOWNLOAD
 2 SQL Injection Vulnerability
2 SQL Injection Vulnerability
That is taking the user ID from the user. As you can see, every ID is linked with a specific user. Let\'s just this template for SQL ... DOWNLOAD
 SQL Injection - Lab #11 Blind SQL injection with conditional responses
SQL Injection - Lab #11 Blind SQL injection with conditional responses
In this video, we cover Lab #11 in the SQL injection track of the Web Security Academy. This lab contains a blind SQL injection ... DOWNLOAD
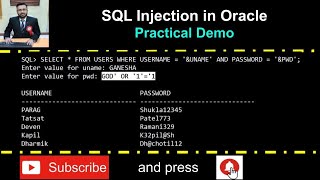 SQL Injection in Oracle with Practical Demo
SQL Injection in Oracle with Practical Demo
Warning: Purpose of this video is to demonstrate SQL Injection practically and it is for education purpose only. It is strongly ... DOWNLOAD
 PostgreSQL Security Features: Episode 6 - SQL Injection Attacks
PostgreSQL Security Features: Episode 6 - SQL Injection Attacks
An SQL #injection attack is an attempt to compromise a database by running SQL statements that provide clues to the attacker as ... DOWNLOAD
 Sql Injection Explained by Example with Express and PostgreSQL
Sql Injection Explained by Example with Express and PostgreSQL
More Software engineering videos https://www.youtube.com/playlist?list=PLQnljOFTspQXOkIpdwjsMlVqkIffdqZ2K Sql injection is ... DOWNLOAD
 15 MCQ Questions with Explanation 🥸 || MS SQL Server Injection 🧐|| MS SQL Server Bulk operations🥹
15 MCQ Questions with Explanation 🥸 || MS SQL Server Injection 🧐|| MS SQL Server Bulk operations🥹
What operation cannot be performed in bulk? Under the which recovery model, all bulk operations are fully logged. DOWNLOAD
 Dangerous Codes: SQLi
Dangerous Codes: SQLi
short #infosec #sql #sqlinjection. DOWNLOAD
 SQL injection attack, querying the database type and version on MySQL and Microsoft
SQL injection attack, querying the database type and version on MySQL and Microsoft
This lab contains an SQL injection vulnerability in the product category filter. You can use a UNION attack to retrieve the results ... DOWNLOAD
 SQL Injection - Lab #11 Blind SQL injection with conditional responses
SQL Injection - Lab #11 Blind SQL injection with conditional responses
In this video, we cover Lab #11 in the SQL injection track of the Web Security Academy. This lab contains a blind SQL injection ... DOWNLOAD
 SQL Injection 101: Exploiting Vulnerabilities
SQL Injection 101: Exploiting Vulnerabilities
shorts. DOWNLOAD
 SQL Injection | Complete Guide
SQL Injection | Complete Guide
In this video, we cover the theory behind SQL injection vulnerabilities, how to find these types of vulnerabilities from both a white ... DOWNLOAD
 SQL injection attack, querying the database type and version on Oracle
SQL injection attack, querying the database type and version on Oracle
Lab: SQL injection attack, querying the database type and version on Oracle PRACTITIONER This lab contains an SQL injection ... DOWNLOAD
 SQL Injection - Lab #10 SQL injection attack, listing the database contents on Oracle
SQL Injection - Lab #10 SQL injection attack, listing the database contents on Oracle
In this video, we cover Lab #10 in the SQL injection track of the Web Security Academy. This lab contains a SQL injection ... DOWNLOAD
 SQL injection attack, listing the database contents on Oracle
SQL injection attack, listing the database contents on Oracle
Lab: SQL injection attack, listing the database contents on Oracle PRACTITIONER This lab contains an SQL injection vulnerability ... DOWNLOAD
 SQL Injection : Data Science Code
SQL Injection : Data Science Code
Avoiding the dangers of SQL Injection. DOWNLOAD
 SQL Injection - Lab #12 Blind SQL injection with conditional errors
SQL Injection - Lab #12 Blind SQL injection with conditional errors
In this video, we cover Lab #12 in the SQL injection track of the Web Security Academy. This lab contains a blind SQL injection ... DOWNLOAD
 SQL Injection - Lab #7 SQL injection attack, querying the database type and version on Oracle
SQL Injection - Lab #7 SQL injection attack, querying the database type and version on Oracle
In this video, we cover Lab #7 in the SQL injection track of the Web Security Academy. This lab contains a SQL injection ... DOWNLOAD
 what is an SQL Injection?
what is an SQL Injection?
Join the NetworkChuck Academy!: https://ntck.co/NCAcademy ☕☕ COFFEE and MERCH: https://ntck.co/coffee #sqlserver ... DOWNLOAD
 SQL Injection Tutorial - Part 2 Database Basics
SQL Injection Tutorial - Part 2 Database Basics
What is SQL Injection?, Recent Breaches, Types of Injection, Tools, Mitigation(Java, Python, Node.js) For more about Cyber ... DOWNLOAD
 Basics of SQL Injection - Penetration Testing for Ethical Hackers
Basics of SQL Injection - Penetration Testing for Ethical Hackers
SQL injection is a common hacking technique used to retrieve or destroy data from a database without permission. It is considered ... DOWNLOAD